Malware analysis Malicious
4.7
$ 19.00
In stock
(260)
Product Description

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

Malware Analysis: Steps & Examples - CrowdStrike

GitHub - filipi86/MalwareAnalysis-in-PDF: Malicious PDF files recently considered one of the most dangerous threats to the system security. The flexible code-bearing vector of the PDF format enables to attacker to carry out

What Is Malware Analysis? Definition, Types, Stages, and Best Practices - Spiceworks

The Differences Between Static and Dynamic Malware Analysis
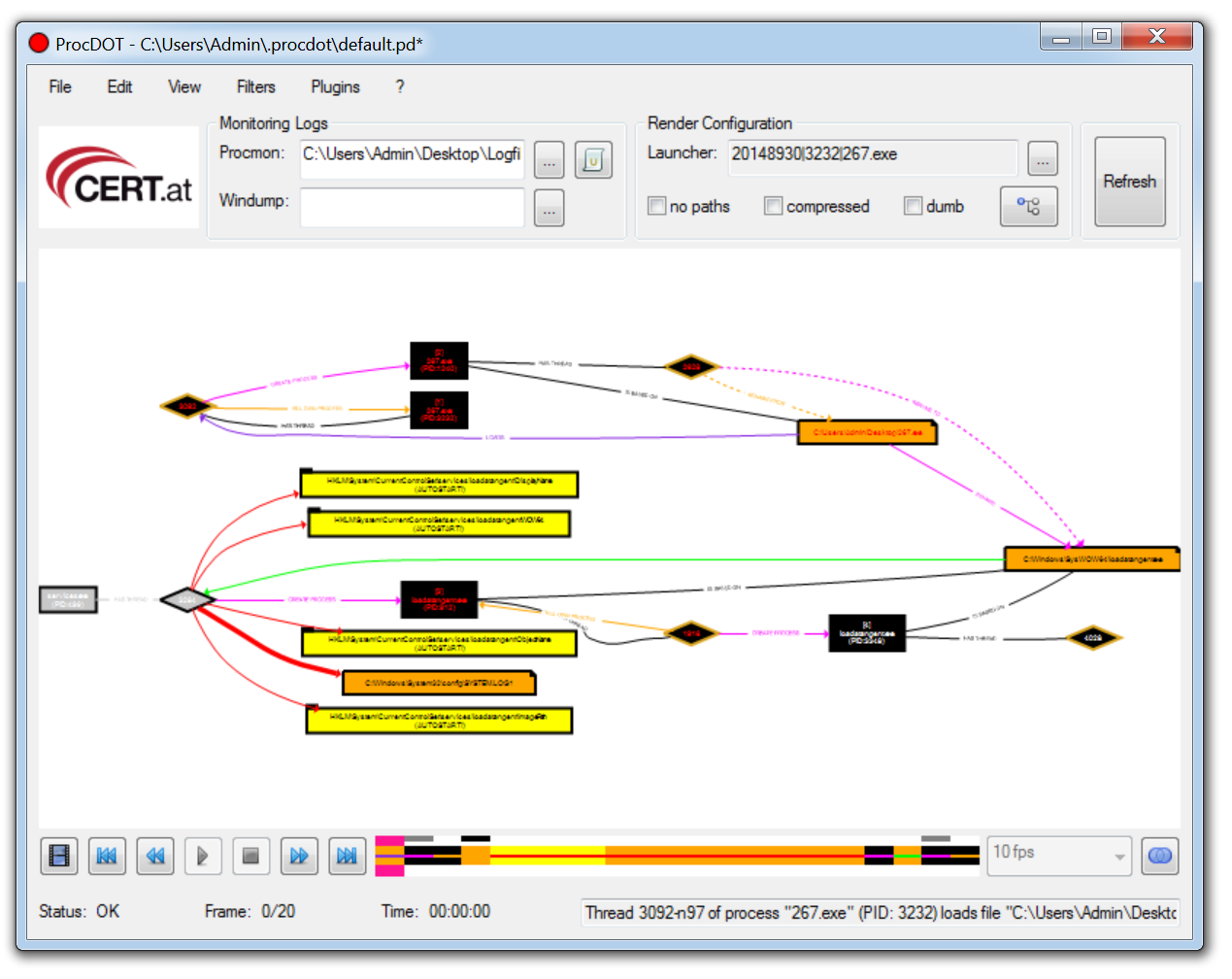
11 Best Malware Analysis Tools and Their Features
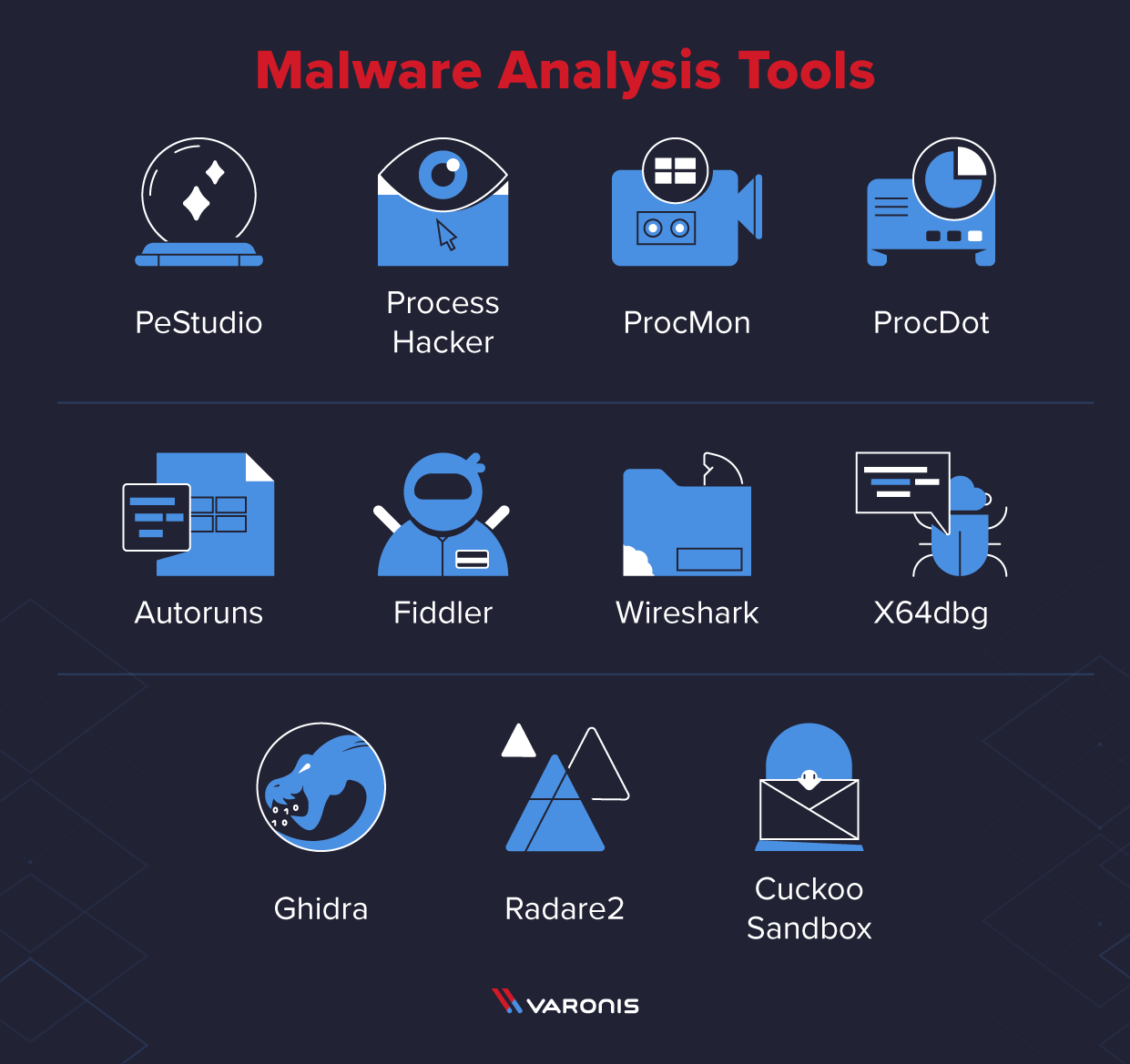
11 Best Malware Analysis Tools and Their Features

Mastering Malware Analysis: A malware analyst's practical guide to combating malicious software, APT, cybercrime, and IoT attacks, 2nd Edition eBook : Kleymenov, Alexey, Thabet, Amr: Kindle Store

A MS word malware analysis Part2: Analyzing malicious macros, by Nishan Maharjan

Malware Analysis: Steps & Examples - CrowdStrike
Practical Malware Analysis: Book review
Highlight, take notes, and search in the book In this edition, page numbers are just like the physical edition

Practical Malware Analysis: The Hands-On Guide to Dissecting Malicious Software
MALWARE ANALYSIS - eForensics